GitOps tools have transformed how teams develop and deploy applications, enabling teams to ship features faster and with greater confidence. Continuing our GitOps series, this piece focuses on the popular tools that help you establish an efficient and reliable GitOps deployment pipeline.
GitOps is an approach where the user can declaratively specify the desired state for both apps and infra in a Git repo. This approach to software development and operations enables teams to collaborate and manage their applications and infrastructure using Git.
By utilizing source control and automation, GitOps automates the entire deployment experience, from code to cloud, providing teams with the ability to manage their applications, infrastructure, and configuration from one centralized location. This has resulted in an improved deployment experience, with more reliable, secure, and faster deployments.
Check out our GitOps Primer article for more information on the basics. This article discusses two essential categories of tools that make GitOps possible - CD and IaC tools.
CD tools for GitOps
These tools enable the main CD pipeline that makes GitOps possible. We are talking about tools that ensure automated deployments in a secure manner and support GitOps Capabilities. These tools also have Kubernetes-native support out of the box.
We will have a future article that provides an in-depth comparison of ArgoCD and FluxCD.
ArgoCD
ArgoCD is a popular open-source solution that’s part of the Argo project. It is a declarative continuous delivery tool for Kubernetes, with a fully-loaded UI and a CLI tool. It stores all configuration logic in Git to allow developers to utilize the code development, review, and approval workflow already connected to Git-based repositories.
Some of its popular features are automating application deployment to target environments, supporting multiple configuration management and templating tools, and enforcing strong authorization with RBAC and multi-tenancy policies. It also offers real-time visibility into application activity, webhook integration, rollouts of complex deployments, access tokens, audit trails, and parameter overrides.
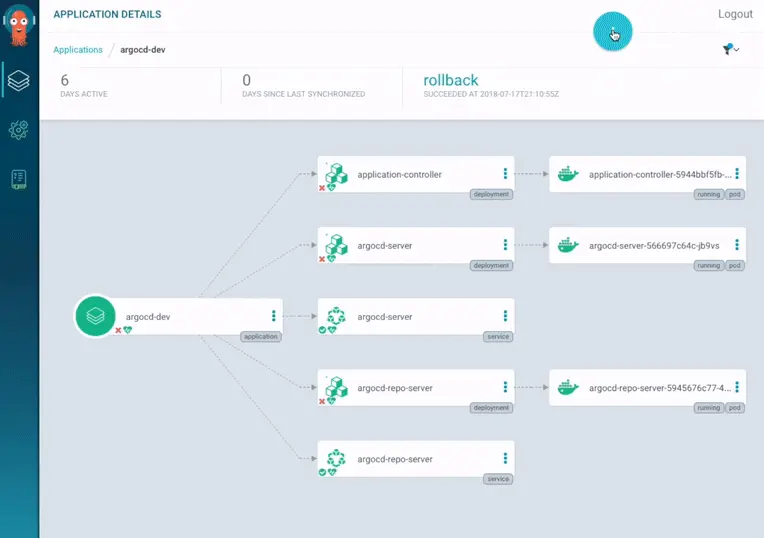
Image source: https://argoproj.github.io/cd/
Flux
Flux is a powerful GitOps tool that helps you manage deployments, resources, and integrations with various Git providers and provides multi-tenancy support. It uses a cluster operator to start deployments in Kubernetes, so there's no need for another CD tool.
It does not require any CI access to your Kubernetes clusters, and it provides atomic and transactional changes with an audit log stored in Git for your convenience and security. Additionally, Flux provides an easy-to-use UI that allows you to track and manage the changes you make to your clusters. Its robustness and scalability make it a great choice for businesses of any size.
Several tools like D2iQ Kommander, Giant Swarm Kubernetes Platform, AWS EKS Anywhere are built on top of Flux.
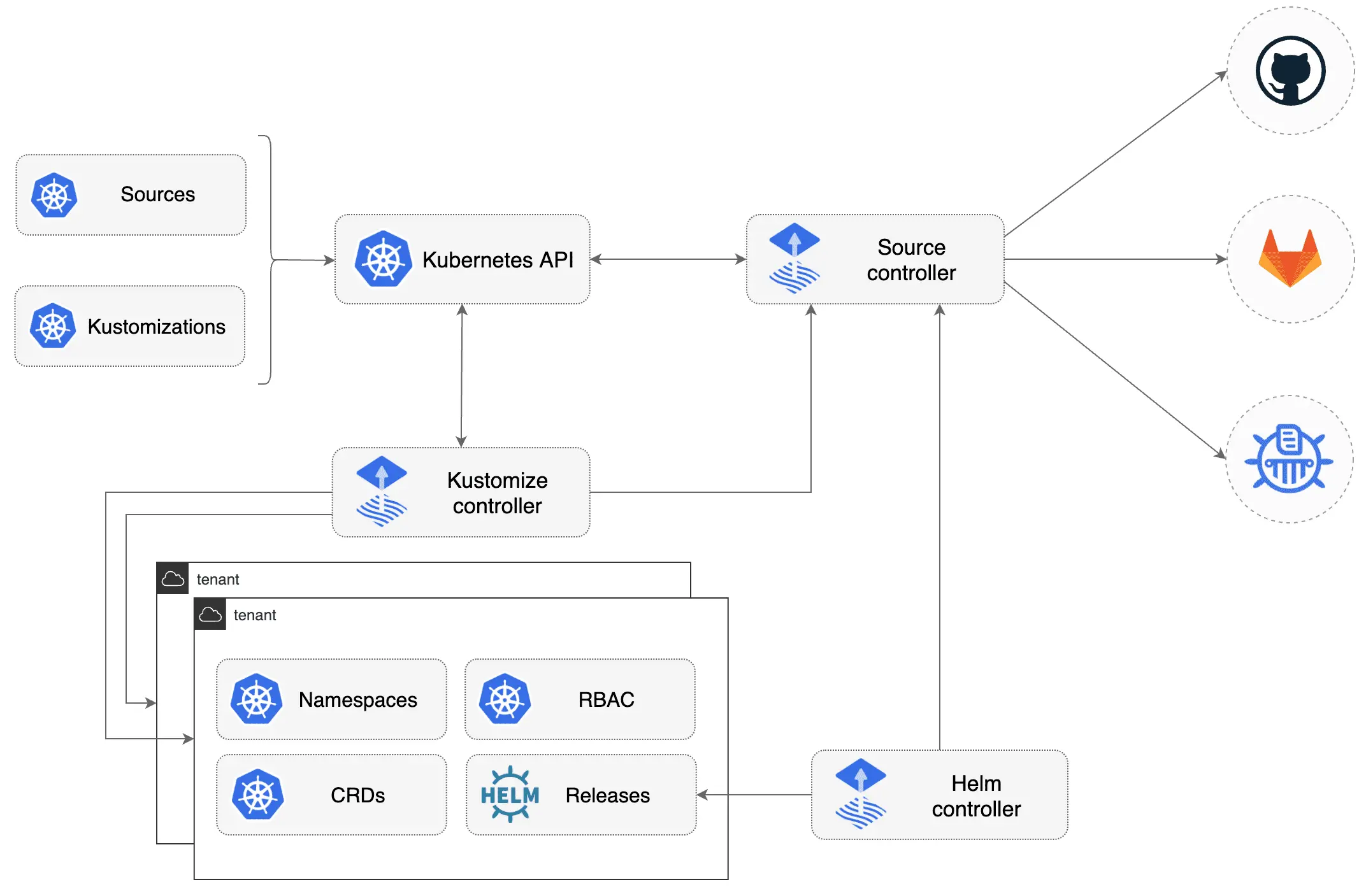
Image source: https://fluxcd.io/flux/
GitLab CI/CD
GitLab CI/CD is a powerful, enterprise-grade CI/CD platform that's designed to help teams create and manage their GitOps pipelines. It provides a number of unique features that make it well-suited for GitOps, such as multi-project pipelines, custom workflows, and the ability to integrate with multiple CI/CD tools. GitLab has also announced its integration of Flux CD.
Additionally, it offers a built-in Kubernetes integration, so teams can leverage the power of Kubernetes to deploy applications and can easily track any changes made to their applications and infrastructure in the CI/CD pipeline. GitLab CI/CD also offers built-in security features, such as authentication and authorization, secrets management, and secure credential storage, that help teams ensure their applications and infrastructure are secure.
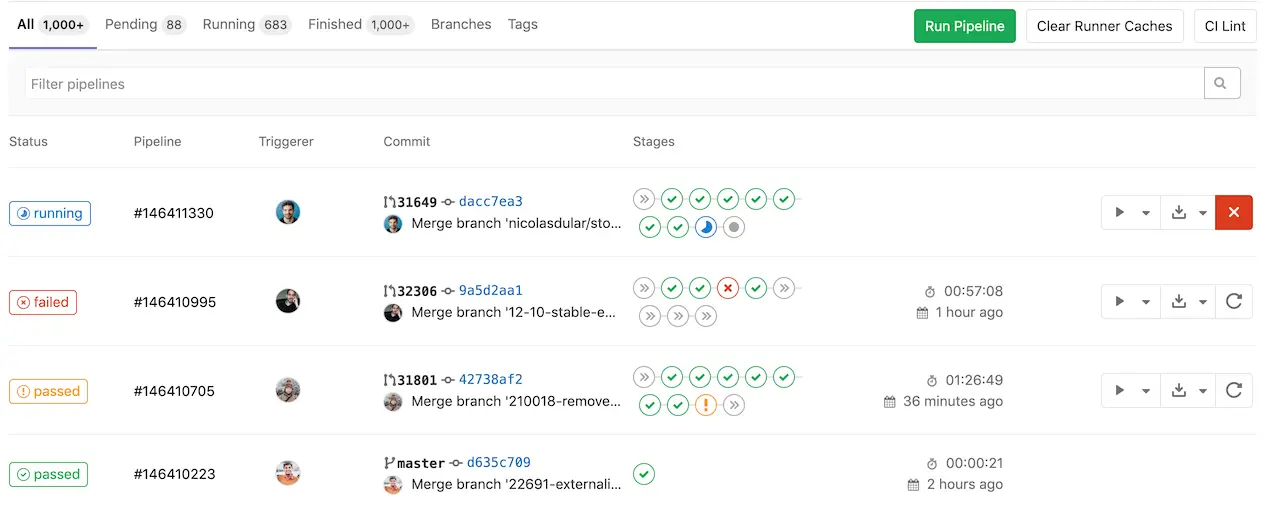
Image source: https://docs.gitlab.com/ee/ci/pipelines/
Werf
Werf is an open-source, GitOps-based CI/CD solution for Kubernetes developed by Flant. It enables teams to quickly and easily deploy their applications and infrastructure with GitOps and Kubernetes. Werf’s features, such as integrated container image building, automated application deployment, and support for multiple cloud providers, make it suitable for GitOps workflows.
Werf is designed to be easy to use and cost-effective, allowing teams to get up and running quickly and without any additional cost. It also offers a number of integrations with popular tools, such as Helm, Kubernetes, and Docker, as well as the ability to connect to multiple Git providers. Additionally, Werf offers support for advanced GitOps features, such as automated rollbacks, secure deployments, and multi-cluster synchronization.
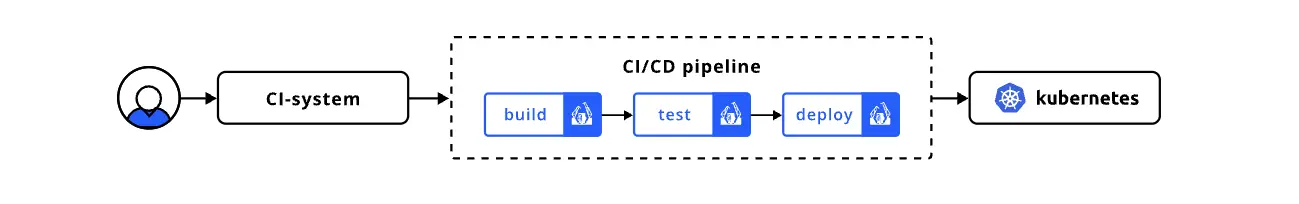
Image source: https://werf.io/
Weave GitOps core
Weave GitOps Core is an extension to Flux. It provides insights into your application deployments and makes CD with GitOps easier to scale and adopt across your teams. It provides a dashboard with applications, sources, and a Flux Runtime view.
Weave GitOps Core is an open-source CD tool for Kubernetes and cloud-native applications that uses Git-based CD, is Kubernetes-native, has declarative automation, and includes integrations with various tools. Weaveworks also provides Weave GitOps Enterprise, a commercial solution based on the open-source Weave GitOps Core, and is also available via the AWS Marketplace.
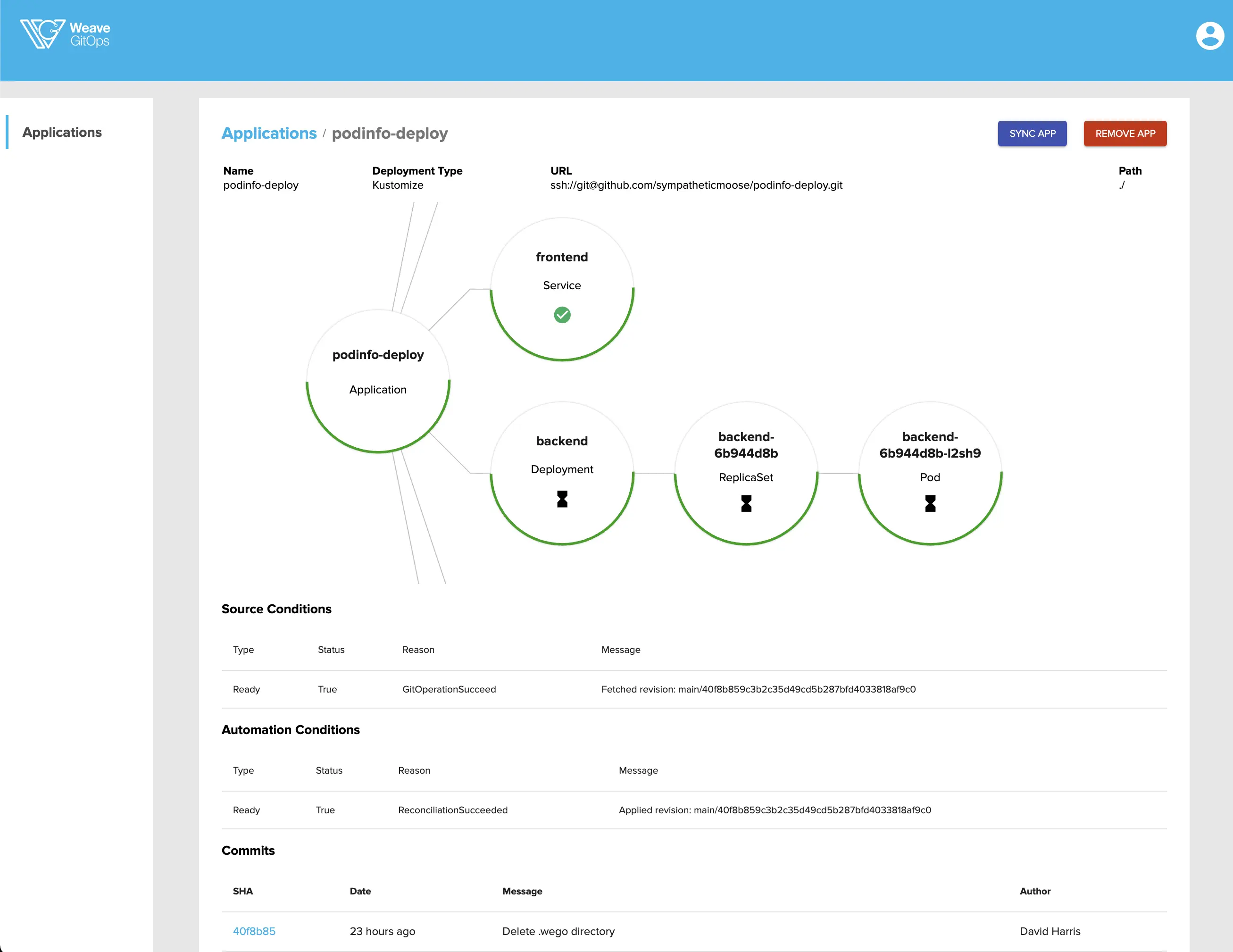
Image source: https://docs.gitops.weave.works/docs/next/gitops-dashboard/index.html
IaC tools for GitOps
Infrastructure as Code (IaC) tools are essential for creating and managing the infrastructure that powers applications and services. The two main advantages of using IaC are that it helps automate the process of configuring and deploying cloud infrastructure and is stored as code, making it easier to version control, track changes, and collaborate on deployments.
In the context of GitOps, IaC tools help teams automate the process of configuring and deploying their applications and infrastructure, ensuring that the same version of the application is deployed in production as in development. This helps teams test the configuration of their applications and infrastructure in a reliable and repeatable manner.
An important thing to note is that IaC tools are not GitOps tools. They are used to create and manage the infrastructure that powers applications and services. However, they can be used in conjunction with GitOps tools to automate the process of configuring and deploying applications and infrastructure. IaC tools in conjunction with a GitOps tool can help teams automate the process of configuring and deploying their applications and infrastructure, ensuring that the same version of the application is deployed in production as in development. This helps teams test the configuration of their applications and infrastructure in a reliable and repeatable manner. Notably, IaC tools do not account for drift by default. However, there are tools that can help you detect and fix drift, with continuous reconciliation. Crossplane has such features built in.
Here are some of the most popular open-source tools. Check out our IaC tools blog for more tools. And here’s an in-depth comparison of CloudFormation, Terraform, and Pulumi.
Terraform
Terraform by Hashicorp is an Infrastructure as Code (IaC) tool that is cloud platform-agnostic and allows users to define cloud and on-prem resources in a human-readable format. It also has plugins that interact directly with cloud providers and SaaS providers, and a registry of publicly available modules. Terraform also enables initializing infrastructure from scratch, defining network resources, and integrating with VCS like GitHub.
It offers features such as an intuitive UI, an extensive library of pre-defined modules, and the ability to define multiple environments for development, staging, and production. Additionally, Terraform supports a wide variety of cloud providers, making it one of the most popular IaC tools.
Pulumi
Pulumi’s Cloud Engineering Platform assists in the Build, Deploy and Manage your infrastructure. Building your IaC using Pulumi allows you to use the languages you love, such as TypeScript, JavaScript, Go, .NET, and YAML to model your cloud infrastructure. It also provides access to a full breadth of services from AWS, GCP, Azure, and over 60 other providers. Your cloud infra code can be reused in the form of Pulumi packages.
Founded in 2017 by Microsoft and Google veterans, Pulumi is a free, open-source infrastructure as code tool. The Pulumi Service offering makes managing infrastructure secure, reliable, and hassle-free. Pulumi service is available as both a self-host or SaaS option. You can easily deliver IaC through your existing CI/CD pipelines. There is also an option to enforce guardrails for security and compliance using policies in standard languages.
You can view the roadmap and contribute to the Pulumi open-source project here. One of their main reasons for success has been their ability to support and help teams migrate to modern containerized, serverless, and Kubernetes workloads easily. Find a detailed comparison between Pulumi and Terraform here.
Crossplane
Crossplane is a framework for building cloud-native control planes without the need to write code. It is built specifically for Kubernetes with support for multi-cloud, serverless, and containerized workloads.
Crossplane provides building blocks that enable you to provision, compose, and consume infrastructure with the Kubernetes API. These individual concepts work together to allow for a powerful separation so that each member of a team interacts with Crossplane at an appropriate level of abstraction.
For enterprises looking for more stability, better support, and reduced risk, there is the Universal Crossplane (UXP) product by Upbound.
Note: Cloud Service Provider (CSP) tools for Infrastructure as Code (IaC) offer an intuitive experience and good integration with existing cloud services. However, they may be limiting if you need to run solutions across multiple clouds.
AWS Cloud Development Kit
AWS Cloud Development Kit (CDK) is an open-source software development framework for defining cloud Infrastructure as Code (IaC) using modern programming languages such as Java, Python, .NET, and TypeScript. This allows developers to create and deploy their infrastructure and runtime code together.
It uses constructs, which are cloud components used to generate AWS infrastructure. AWS CloudFormation powers the provisioning, and you get all the benefits of CloudFormation, including repeatable deployment, easy rollback, and drift detection.
Some of its drawbacks and limitations are that AWS CDK does not currently have support for non-AWS cloud providers, so teams using it will be limited to AWS cloud services. AWS CDK is a relatively new tool, and it may still have some bugs and lack certain features that teams may need. You might need to use other IaC tools, such as Terraform, to supplement.
GCP Cloud Deployment Manager
Google's Cloud Deployment Manager is an infrastructure deployment service that automates the creation and management of Google Cloud resources. It provides users with the power to write flexible templates and configuration files, allowing them to create deployments that include various Google Cloud services, such as Cloud Storage, Compute Engine, and Cloud SQL.
Through the use of these files, users can deploy the resources they need and configure them to work together seamlessly, providing them with an easy and efficient way to manage their cloud infrastructure. Additionally, Cloud Deployment Manager allows users to make changes and updates to their deployments quickly and easily, ensuring that their cloud resources remain up-to-date and in line with their desired configurations.
Azure Resource Manager
Azure Resource Manager is the deployment and management service for Azure. It acts as a management layer that authenticates and authorizes requests from your Azure APIs, CLI, or SDKs before forwarding them to the respective Azure service. Operations such as creating, updating, and deleting Azure resources are supported, and features like access control, locks, logs, and tags help you organize your resources after deployment.
To implement Infrastructure as Code (IaC) for your Azure cloud resources, you use Azure Resource Manager (ARM) templates. These IaC templates are written in Bicep, a domain-specific language with declarative syntax. The Bicep code is converted into JSON files during deployment by the Bicep CLI. ARM templates can also be written directly in JSON.
Azure resources that share a common lifecycle are grouped into resource groups. You can then deploy to the target resource group. All the available resources for Azure services can be found here.
Considerations before using GitOps
To make the most out of GitOps, you will need a process and tooling shift. Here are some practical considerations before adopting GitOps.
- Ensure that everyone in the organization is properly trained on the tools and processes used in the GitOps workflow (Git, CD tools, IaC, and Kubernetes).
- Establish a clear policy for committing and merging changes into the repository. Especially when it comes to testing and reviewing the changes before they are committed. Make sure the conflicts or issues are identified and resolved quickly.
- Maintain the security of the Git repository carefully with the right access controls, proper authentication and authorization, and how secrets or sensitive data are securely stored and managed.
- Proper monitoring and backups of the Git repository are essential. This helps to ensure that any changes can easily be tracked and reverted if necessary.
- Most often, choosing an open-source tool with an active community and support for multiple cloud vendors is the safer option. As it saves debugging time, is extensible, and can scale with your organization.
By taking the proper precautions and ensuring that everyone is properly trained and equipped with the right tools, organizations can reap the benefits of using GitOps and have a smooth and successful transition into the GitOps workflow.
Conclusion
GitOps is a powerful approach to software development and operations that helps teams collaborate and manage their applications and infrastructure using Git. It automates the deployment experience and helps teams achieve improved deployment experiences with more reliable, secure, and faster deployments.
We have this article provided you with an overview of some of the most popular tools and has helped you understand the benefits of GitOps and the tools available to help you adopt it.
Argonaut is a deployment automation tool that comes with all the benefits of IaC and CI/CD tools in-built. We follow GitOps best practices, provide a secret-management solution, and keep your configurations stored in your repo. Moreover, we have monitoring built-in for cluster and app-level metrics, along with providing access to multiple runtimes, environments, applications, and infra from a centralized dashboard.


